Let me paint you a picture. You're the security guard of a massive office building — 500 floors, 10,000 employees, hundreds of entry points. Every second, thousands of things are happening. Doors opening. Badges being scanned. Printers being used. Emails being sent.
Now imagine trying to watch all of that manually. You'd miss stuff. A lot of stuff. And that one thing you miss? That might be the hacker who just walked in wearing a fake badge.
This is exactly the problem that SIEM was built to solve.
What you'll learn in this post: What SIEM actually is, why it exists, how it works, what it looks like in real life, and whether you should care about it. Spoiler: you should.
01 — So... What Even Is SIEM?
SIEM stands for Security Information and Event Management. Big words. Simple idea.
At its core, a SIEM is a system that collects logs from everything in your network — servers, firewalls, applications, user accounts, cloud services — and then analyses them in real time to spot anything suspicious.
The best analogy: Think of SIEM as the brain of your security operation. It doesn't stop threats itself, it sees them, understands them, and alerts the humans who can act on them.
Before SIEM existed, security teams had to manually check dozens of different systems for suspicious activity. Your firewall logs were in one place. Your Active Directory logs were somewhere else. Your web server logs were on a completely different machine. Nobody had time to connect the dots.
SIEM changed the game by centralising everything into one place and doing the pattern-matching for you.
02 — The Two Big Jobs of SIEM
The name gives it away — SIEM does two things. Let's break them down:
SIM — Security Information Management
Collects and stores logs long-term
Creates a historical record of everything
Used for forensics after an incident
Helps with compliance (GDPR, ISO 27001)
Answers "what happened last Tuesday at 3am?"
SEM — Security Event Management
Monitors events in real time
Correlates events across multiple systems
Triggers alerts when rules are matched
Answers "is something happening RIGHT NOW?"
The part that wakes SOC analysts up at 2am
Together, they give you full visibility — both a live view of what's happening and a complete history you can dig into later.
03 — How Does It Actually Work?
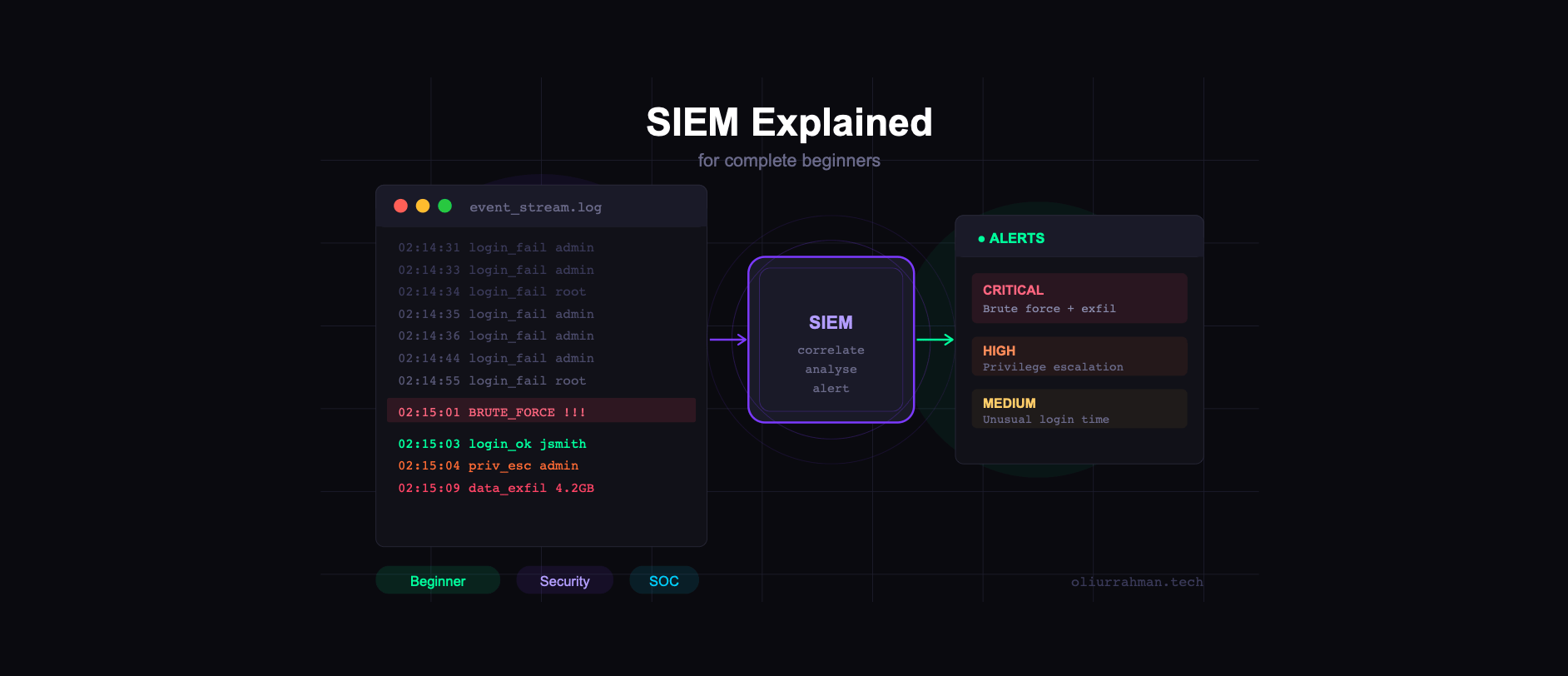
Here's the SIEM workflow in plain English:
Step 1 — Data Collection Logs pour in from everywhere — firewalls, servers, endpoints, cloud apps, Active Directory. The SIEM ingests all of it via agents or syslog.
Step 2 — Normalisation All those logs come in different formats. The SIEM translates them into a common language so they can be compared. This is called parsing.
Step 3 — Correlation The SIEM looks for patterns across events. One failed login = normal. 500 failed logins in 60 seconds from one IP = brute force attack. Fire the alert.
Step 4 — Alerting When a correlation rule is triggered, an alert is raised. A SOC analyst reviews it and decides: real threat, or false positive?
Step 5 — Storage & Reporting Everything is stored long-term for forensics, compliance reporting, and future threat hunting. Nothing gets thrown away.
04 — A Real-World Example
Let's say a hacker is trying to break into your company. Here's how SIEM catches them:
# 02:14:33 — SIEM starts seeing something weird...
EVENT: Failed login attempt → user: admin IP: 185.220.101.47
EVENT: Failed login attempt → user: admin IP: 185.220.101.47
EVENT: Failed login attempt → user: root IP: 185.220.101.47
EVENT: Failed login attempt → user: admin IP: 185.220.101.47
# ... 496 more failed attempts in 58 seconds ...
# Correlation rule triggered: BRUTE_FORCE_THRESHOLD
⚠ RULE MATCH: 500+ failed logins from single IP in <60s
# 02:15:01 — Something even worse happens...
EVENT: Successful login → user: jsmith IP: 185.220.101.47
EVENT: Privilege escalation → jsmith → Administrator
EVENT: Large data transfer → 4.2GB to external IP
CRITICAL ALERT: Account compromise + data exfiltration detected
Ticket #INC-2847 created → Assigned to: SOC Analyst on dutyWithout SIEM, those 500 failed logins would be scattered across different server logs that nobody was watching. With SIEM, an alert fires within seconds of the pattern being detected.
SIEM doesn't just collect noise. It finds the signal hidden inside the noise.
05 — What Do SOC Analysts Actually Do With It?
If you're thinking about a career in cybersecurity, you'll spend a lot of time staring at a SIEM dashboard. Here's the honest day-to-day reality:
A typical SOC analyst's morning: Log in. Open SIEM dashboard. See 47 alerts from overnight. Start triaging — is this a real threat or a false positive? Investigate the suspicious ones. Write up your findings. Repeat until coffee runs out.
The main tasks are:
Triage — deciding which alerts are worth investigating and which are false positives. Spoiler: most alerts are false positives. This is both the art and the frustration of SOC work.
Investigation — digging into an alert to understand what actually happened. You'll pivot through logs, look at timelines, trace a user's activity across systems. It's like being a detective, but with better tools and worse hours.
Threat hunting — instead of waiting for alerts, proactively searching the SIEM for signs of threats that haven't triggered any rules yet. This is the advanced, fun part.
06 — Popular SIEM Tools You Should Know
These are the big names you'll encounter in job descriptions and in the wild:
Tool | What it's known for |
|---|---|
Splunk | Industry standard. Powerful but expensive. |
Microsoft Sentinel | Cloud-native. Big in enterprise. |
IBM QRadar | Enterprise favourite. Deep analytics. |
Elastic SIEM | Open source friendly. Great for home labs. |
Wazuh | Free & open source. Perfect for learning. |
AlienVault OSSIM | Free version available. Great starter. |
Want to practice? Set up Wazuh or Elastic SIEM in a home lab — both are free. Throw some suspicious traffic at it and watch the alerts fire. This is hands-down the best way to learn SIEM before landing your first SOC job.
07 — Common Misconceptions
Let's kill a few myths before you walk away with the wrong idea:
Myth: "SIEM will automatically stop attacks." Nope. SIEM detects and alerts. It doesn't block anything by itself. That's what firewalls, EDR tools, and humans are for.
Myth: "If SIEM doesn't alert, you're safe." Also nope. SIEM only catches what it's been told to look for. A sophisticated attacker who moves slowly and carefully can fly under the radar. Hence why threat hunting exists.
Myth: "SIEM is plug-and-play." Absolutely not. A SIEM requires constant tuning — writing rules, reducing false positives, adding new log sources. It's a tool that needs a human to get the best out of it.
08 — Should You Learn SIEM?
If you want to work in a SOC, as a security analyst, or in incident response — yes, 100%. SIEM is the central nervous system of most security operations centres. It'll be on almost every job description you read.
Even if you're going into pentesting or red teaming, understanding SIEM makes you better at your job — you'll know what defenders can see, which helps you move more stealthily.
Where to start: HackTheBox Academy has a great Security Monitoring & SIEM Fundamentalsmodule. TryHackMe has several SOC-focused learning paths too. Both are beginner-friendly and hands-on.
TL;DR — The 60-second version
SIEM = centralised log collection + real-time threat detection
It collects logs from your entire network and looks for suspicious patterns
When a pattern matches a rule, it fires an alert for a human to investigate
It's the most important tool in a SOC analyst's toolkit
Popular tools: Splunk, Microsoft Sentinel, Elastic, Wazuh
SIEM detects — it doesn't block. Humans still need to respond
Best way to learn: spin up Wazuh in a home lab and play with it
If this post helped you understand SIEM, share it with someone who's trying to break into cybersecurity.
— Oliur Rahman